How MSPs Use Cybersecurity Alerts to Detect SaaS Breaches
The Superpower of Security Alerts in the MSP World
MSPs are the unsung heroes in the dynamic world of IT management, keeping the digital gears turning smoothly for clients. But as every superhero knows, staying vigilant of potential threats is the secret to victory.
Security alerts are an MSP’s reliable sidekick in the quest to stay one step ahead of malicious actors. Think of them as your personal signal flare, ensuring you’re always in the loop when IT hiccups arise.
The 2023 Global Risks Report by the World Economic Forum ranked widespread cybercrime and cyber insecurity as the eighth most severe global risk within a two-year period. A security alerting system that sends expertly analyzed and actionable notifications can help you detect suspicious activities and mitigate cyber risks such as malware, data breaches or business email compromise.
In this blog, we will guide you through this world of security alerts and how you can leverage them to keep your managed systems running without a hitch.
What Is a Security Alert?
A security alert is an automatic notification sent to organizations when a potential threat or breach is detected. These notifications — sent via email, text or direct integration with MSP’s service automation systems — allow users to take immediate steps against an intrusion or threat to safeguard their network and data.
At SaaS Alerts, the building block of security alerting is known as an “event” that captures a user’s action, such as uploading files, opening a file or executing a standard login. Often referred to as user or system log events, many platforms discard these actions, deeming them unimportant. But we preserve and monitor these logs for a year for each of our MSP partners for two major reasons:
- Standalone actions aren’t intriguing in isolation. For instance, one file upload is not alarming, but downloading 500 files in 10 minutes is a story. We deploy machine learning to detect the subtle shifts from average to noteworthy actions.
- Change in user behavior helps with alert categorization. We decipher how individuals typically navigate and then spot the moments they step out of their patterns of behavior. SaaS Alerts uses application logic and intelligence to rank these activities according to their severity:
-
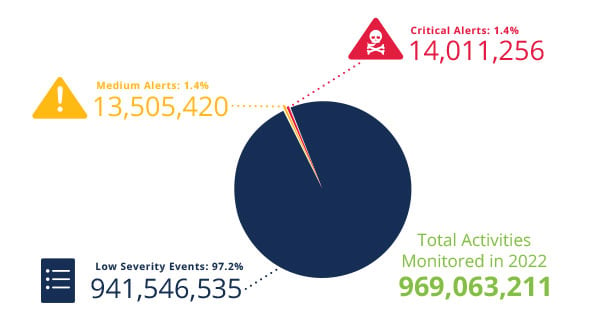
- Low: These security events are of little concern but they do present valuable information about user behavior, organizational policy, product utilization and data exfiltration risk.
- Medium: These alerts do not always require immediate action or pose an imminent risk. Prompt investigation, however, can ensure that security is in place and account activity is continually monitored for potential risk.
- Critical: While less than 1% of events rise to the level of critical alerts, the consequences of even a single successful compromise can lead to significant financial losses for any business.
Our 2023 SaaS Application Security Insights (SASI) Report found that low severity events accounted for 97% of the 970 million activities we monitored last year, indicating that activities requiring immediate investigation (medium and critical alerts) are comparatively minimal. Still, reviewing low severity events can be helpful as a security hygiene measure.
Cybersecurity Alerts MSP Businesses Should Set up and Why
When it comes to detecting suspicious activities, these three alerts are a superhero squad for MSPs:
1. Privileged User and Account Monitoring
Privileged user accounts are a backstage pass to an organization’s network or software. IT administrators often use these accounts to maintain and control the organization’s tech infrastructure. If these accounts fall into the wrong hands, they can let attackers sneak in and swipe sensitive stuff.
To minimize these risks, you can set up alerts when there’s a successful privileged account login from:
- Outside of an approved location
- Outside of an approved IP address range
- Using a new or unapproved device
If a malicious actor successfully accesses a privileged account, they can maneuver past firewalls and security barriers, wreaking havoc on your security framework and accessing critical business data. Despite the high consequences of a privileged account breach, a report by Cybersecurity Insiders found that 49% of organizations continue to have users with more access privileges than necessary.
2. Data Exfiltration
Data exfiltration is like a stealthy act of burglary that can infiltrate the IT environment of your client to steal their most valuable asset — sensitive information — and contribute to significant financial losses. In fact, the global average cost of a data breach was $4.45 million in 2023, according to an IBM report.
Data exfiltration leaves traces, such as unusual spikes in data transfers, access from unfamiliar locations or a sudden flood of outbound traffic. The following security alerts can pick up digital clues and sound the alarm before the real damage is done.
- File download limit exceeded: Setting up an alert that informs when the limit of file download exceeds a pre-set threshold can indicate excessive file activity and possible data exfiltration risk.
- File accessed outside approved location: Setting up an alert that informs when a user outside an approved location has successfully opened or downloaded a file.
File shared and accessed anonymously: Setting up an alert that informs when an anonymous link is generated to share files and provide access without requiring proper authentication.
3. Breaching Attempt Detected
Brute force attacks are used by cybercriminals to access accounts by guessing possible combinations of a targeted account password until the correct password is discovered. On average, SaaS Alerts sees approximately 40,000 brute force attacks daily across our user base.
To be aware of the possibility of a brute force attack by a malicious actor, you need to engage a third-party 24/7 automated security alerts tool that offers:
- Account locked alert: Indicating there have been multiple unsuccessful attempts to login into a specific account. While this alert can often occur due to an end user forgetting their password, it could also be the result of malicious behavior.
- Multiple authentication failures alert: Informing when account credentials are entered incorrectly multiple times within a short period. This alert might indicate a user struggling with correct login information or a potential unauthorized access attempt.
Moving from Alerts to Remediation
While security alerting is a crucial indicator of potential threats, MSPs require a solution that also translates the alerts into actionable responses. The Respond module offered by SaaS Alerts makes it easy for MSPs to create rules that automatically remediate detected threats.
Automated remediation steps help in:
- Reducing the time between threat detection and response
- Minimizing the chances of human error
- Optimizing human resource allocation to focus on critical tasks
The journey from alerts to remediation is not just about closing the gap between detection and action; it’s about reprioritizing your cybersecurity activities from a reactive to a proactive model.
Leveraging SaaS Alerts for Proactive Cybersecurity
With our SaaS security platform, implementing an alert system is like tuning a musical instrument – setting thresholds at the right level to avoid constant alarms. Each client’s policies are unique, so we aid MSPs in establishing their own indicators of compromise (IOCs).
Tailored IOCs offered by SaaS Alerts allow MSPs to align with each client’s operations. For instance, 500 file downloads in one hour can trigger an IOC for one client but not for another.
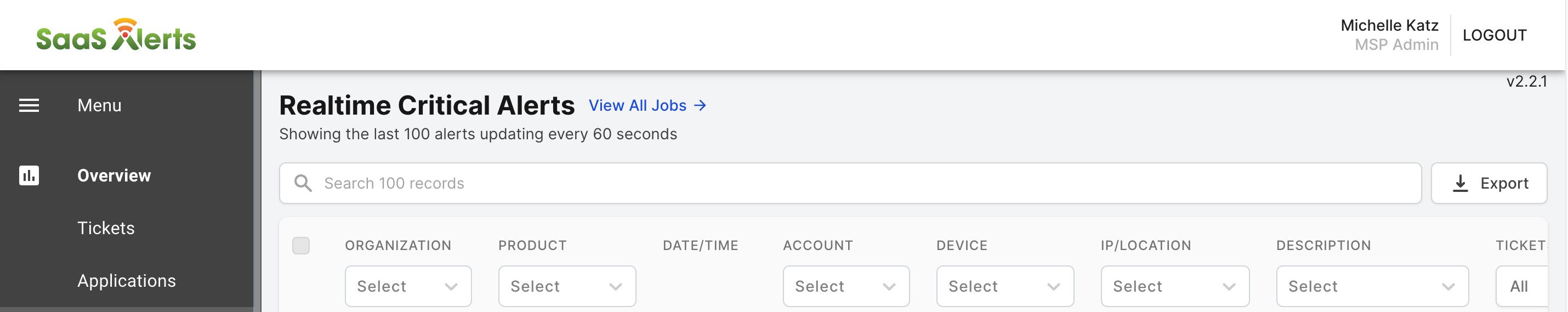
To make security alerts more specific, our three categories of alerts (critical, medium, low) can be further filtered down based on:
- Organization name
- Product type
- Individual accounts
- Device type
- IP/location
- Description of event (e.g., authentication success event, file download limit event)
By prioritizing security alerts and automating responses, our toolset is a vigilante sidekick that saves MSP heroes from bad actors and alert fatigue.
Request a personalized demo to see SaaS Alerts in action.







